Cyber warfare is evolving rapidly, and the latest example is both alarming and illustrative of the complexities in today’s digital battleground. A relatively new group known as TeamPCP has emerged, leveraging well-known vulnerabilities to conduct attacks that have struck at the heart of geopolitical tensions by targeting Iranian systems. In a twist that merges cybercrime with political motives, they are deploying a worm designed to wipe data on systems configured for Iran, showcasing both scale and sophistication.
The Emergence of TeamPCP
Since its inception in December 2025, TeamPCP has focused on compromising corporate cloud environments using a self-propagating worm that specifically drills into exposed cloud infrastructure. According to analyses by the security firm Flare, their attacks predominantly target the cloud, with over 97% of affected servers attributed to platforms like Azure (61%) and AWS (36%). The group’s strategies don’t lean on novel exploits but rather on a combination of industry-standard tools and targeted automation, which some experts argue transforms mere vulnerabilities into a highly efficient exploitation mechanism.
The Wiper Campaign: CanisterWorm
The latest campaign, centered around a malicious payload dubbed CanisterWorm, marks a significant escalation. Reports suggest that the worm can detect if a system is set to Iran's timezone or uses Farsi as its primary language. If confirmed, it launches a wiper attack capable of erasing data across all nodes in a dedicated Kubernetes cluster. If the conditions aren’t met, it defaults to wiping the local system, creating potential chaos for companies operating in or engaging with Iran.
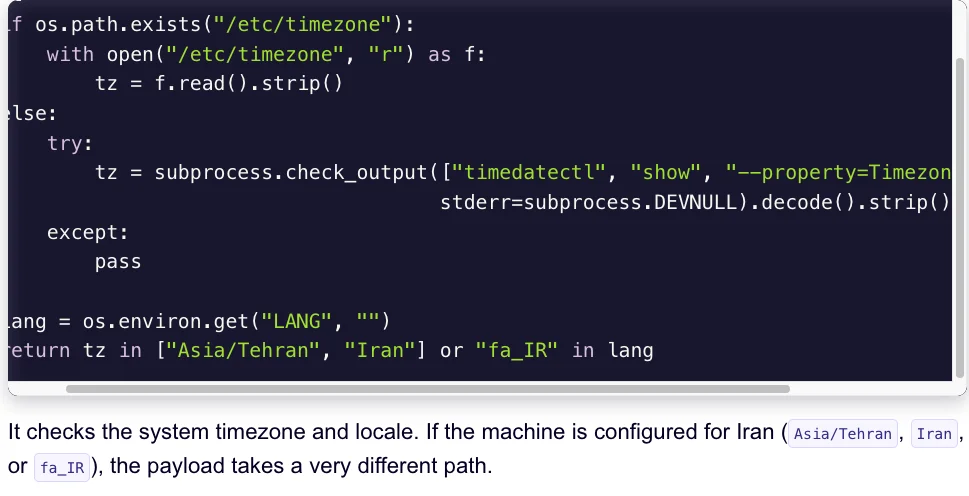
A snippet of the malicious CanisterWorm that targets data on Iranian systems. Image: Aikido.dev.
Supply Chain Attacks as a New Frontier
A key facet of TeamPCP’s strategy came into sharp focus with their recent attack on the vulnerability scanner Trivy from Aqua Security. The group managed to integrate credential-stealing malware into official releases on GitHub actions, illustrating how supply chain vulnerabilities can be exploited on a massive scale. Aqua Security confirmed that they have removed the harmful files, but the scope of the breach raises significant concerns about persistent threats lurking in popular development tools.
Experts emphasize that compromising tools like Trivy not only affects the immediate targets but can have ripple effects throughout the software development ecosystem, given the widespread use of such scanners. Indeed, the link between infrastructure security and application supply chain integrity has never been more apparent; it's a troubling convergence that organizations must confront.
Visibility vs. Anonymity
Interestingly, the attackers behind TeamPCP appear to revel in their notoriety. Reports indicate that they have used Telegram to boast about their capabilities and accomplishments, including claims of data theft from large multinational corporations. This raises a critical question about threat motivations: Are they purely financially motivated, or is there an element of political statement woven into their actions? Observers also note that their behavior resembles that of 'chaotic evil' actors, leveraging digital platforms for both destructive purposes and psychological warfare.
Image: Aikido.dev.
Addressing the Growing Threat
As supply chain attacks proliferate, organizations must begin to rethink their security postures. Catalin Cimpanu highlights in a recent newsletter that the volume of attacks through this vector has surged in recent months, and while security firms are becoming more adept at detecting them, the architectural challenges of platforms like GitHub remain significant. The ability to quickly identify and remediate compromised repositories on a platform designed to promote code sharing complicates the response mechanism.
The reality is that cyber threats like those posed by TeamPCP require an evolved understanding of threat intelligence and incident response. It’s clear that traditional security measures must be supplemented by strategies specific to cloud-native applications and supply chain integrity. Companies need to ensure their cloud configurations are locked down and adopt a zero-trust approach to their environments.
Conclusion: A Wake-Up Call
This escalating tension brought forth by TeamPCP serves as a wake-up call for organizations operating in sensitive geopolitical scenarios. Cyber resilience is no longer just an IT conversation; it's a business imperative that demands attention at the highest levels. Failure to address these emerging threats could result in catastrophic data loss and an erosion of trust that could take years to rebuild. If you're in this space, now’s the time to reassess vulnerabilities, enhance monitoring, and stay vigilant against evolving cyber threats.
